There seem many different ways to set up WinRM looking at web site after web site on the Internet. Some seem very complicated and almost a chicken and egg situation. Although this looks like a long read, it’s swift and easy to set up WinRM, once you have the idea of how to do it. So please read through.
Where to Start!
Lets quicky look at the Terraform code and understand what we need to do to make the virtual machine setup WinRM for us.
If you look at the Terraform documentation for Azure_Windows_Virtual_Machine , you will see a winrm_listener block section. (fig1)
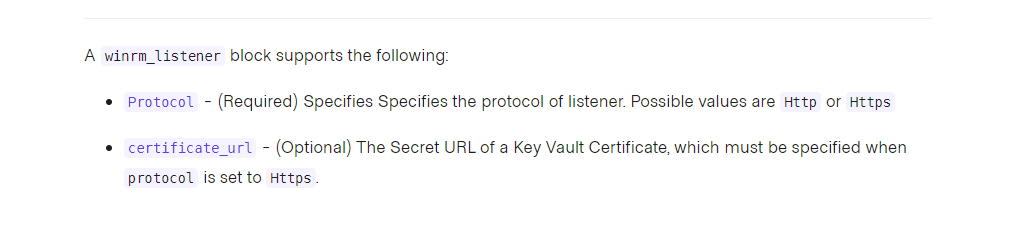
On first impression, it looks like that’s all you need, choose a protocol (always HTTPS) and then specify the path to the Key Vault certificate. But beware, if you look closely, it’s after the SECRET URL of the certificate.
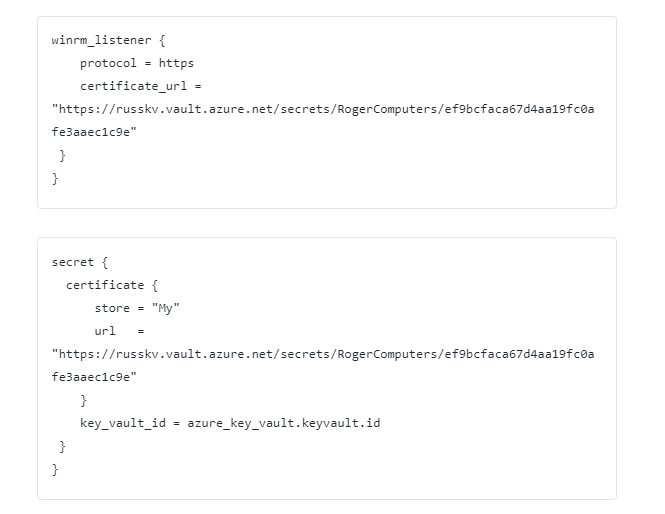
However, this isn’t all you need, you need the secret block as well. (fig2)

and a certificate block (fig3), which sits inside the secret block.

Now I know this is starting to sound complicated but stick with me on this. It’s easier once you have seen the code (fig4) (here’s one I made earlier)
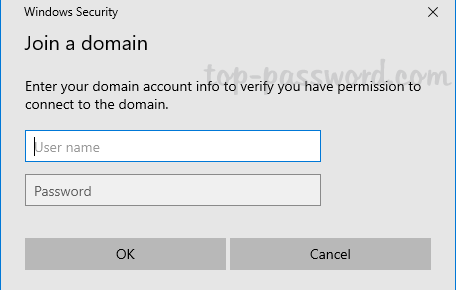
Note: Do not just setup Http, although it is encrypted, this is if you are connected a machine that is part of Active Directory. A lot of machines that I work on are not part of AD, and therefore you need to use the HTTPS to secure the connection.
Continued on the next page